We've established that CI/CD doesn't evolve external systems, that Change-as-Code gives us a discipline for managing that evolution, and that systems are shaped by their path, not their snapshot.
This post is about what happens when you accept all of that — and still don't have anything governing the sequence across boundaries. Each tool handles its own scope well. But maturity in the parts doesn't guarantee coordination of the whole. In fact, it often masks the gap, because each subsystem works well enough in isolation that nobody notices the spaces between them.
Here's what that looks like in practice.
A real incident
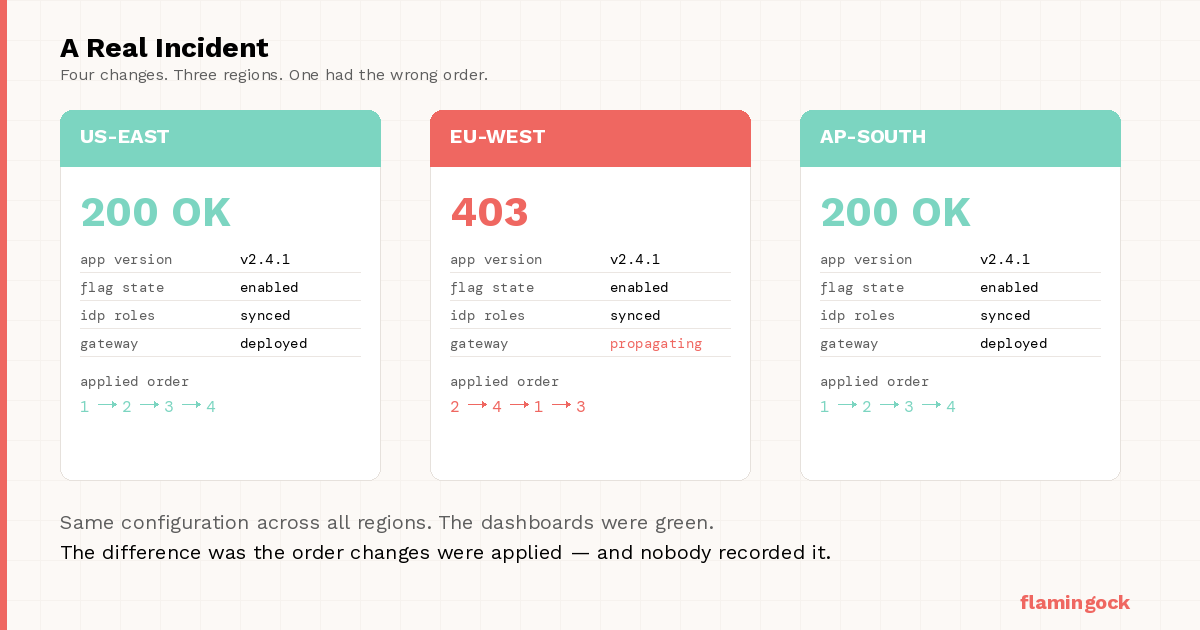
Users in EU-West are getting 403s on endpoints that work fine in US-East.
The platform team checks the obvious things. Application version: same everywhere. Feature flag state: consistent. IdP role mappings: correct. API gateway policies: deployed.
Everything matches. The dashboards are green. And yet behavior diverges by region.
It takes hours to find the cause — not because anything is broken, but because nothing appears to be.
Here is what actually happened.
The rollout involved four coordinated changes: new role definitions in the application, updated role mappings in the external identity provider, revised API gateway access policies, and a feature flag to activate the new authorization logic.
The plan was sequential: IdP first, then the application deploy, then gateway policies, then the flag.
But the plan was not the system.
The IdP team pushed their role mapping update ahead of schedule. The feature flag was enabled before gateway policy propagation had completed globally. Gateway updates rolled out regionally, with EU-West lagging behind.
By the time anyone looked, every system had converged. Same snapshot. Same configuration. No trace of the sequencing failure — because no system was recording sequence in the first place.
The 403s were not caused by a bad deployment or a wrong configuration. They were caused by the right changes arriving in the wrong order, in a system with no way to know that order mattered.
This pattern is not unusual. Azure Front Door experienced a global outage in October 2024 when configuration metadata passed all health checks during staged rollout but triggered asynchronous data-plane crashes after propagation. AWS users have reported API Gateway key-to-policy associations taking hours to propagate regionally, with correct configuration in place but incorrect runtime behavior. In each case, the snapshot was valid. The path was not.
What would have been different with an execution layer?
Before describing the alternative: an execution layer is not a workflow engine or an orchestration platform. It is a runtime-aware architectural capability — one that captures, orders, and makes inspectable the cross-boundary changes a system undergoes as it evolves. Think of it less as a tool and more as a structural concern, the way observability became one.
If an execution layer had existed, this rollout would not have been treated as four independent actions. It would have been treated as a declared evolution sequence — a single, ordered plan with verification between steps:
Step 1: IdP role mapping update
Step 2: Application deployment
Step 3: Gateway policy update (global propagation confirmed)
Step 4: Feature flag activation
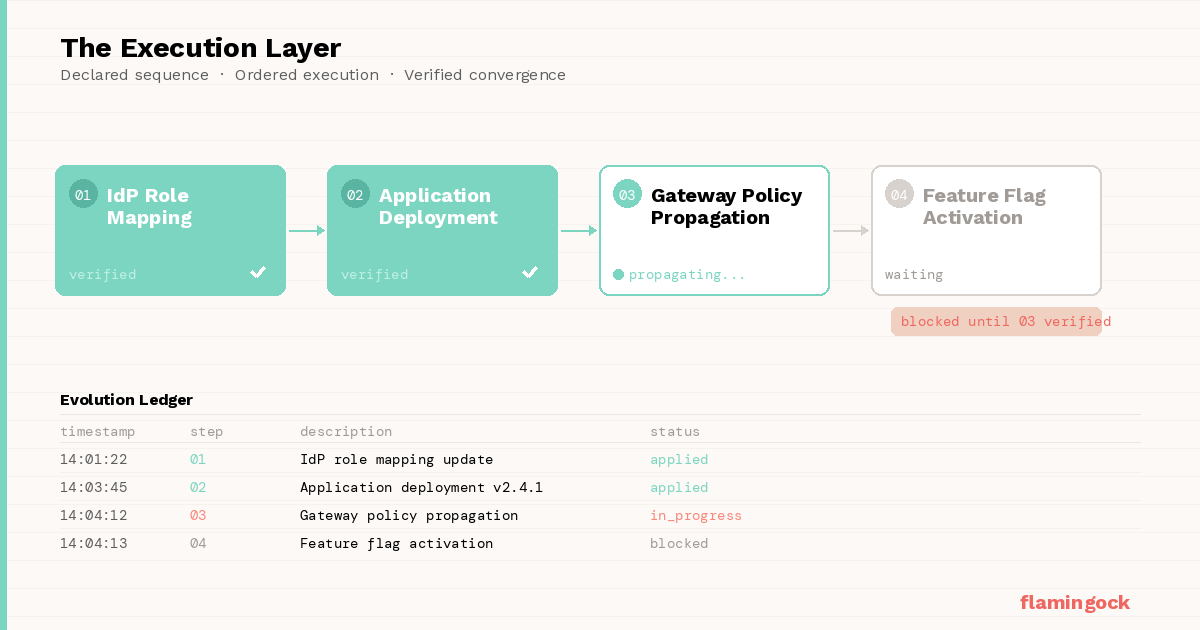
Each step would be executed in order, recorded in a central evolution ledger, and require readiness verification before the next could advance. The feature flag could not have been activated until gateway propagation was confirmed globally. The early IdP push would have been visible as an out-of-sequence mutation. Regional inconsistency would have blocked progression rather than silently becoming a runtime issue.
Most importantly, the system would retain a complete, queryable record of how it evolved — not just where it ended up. The gap would have been caught at execution time instead of surfacing hours later through behavioral anomalies.
This is not without cost. An execution layer means new coordination overhead, sequence contracts across team boundaries, and one more system-level concern to maintain. The question is whether that cost is lower than the cost of undiagnosed path divergence. In distributed, regulated, or high-trust systems, it usually is — and it's usually not close.
The architecture had delivery orchestration. What it lacked was evolution governance — and those are fundamentally different capabilities.
The layer nobody defines
Most systems explicitly define an application layer, an infrastructure layer, and a delivery layer. Very few define an explicit execution layer for system evolution — a runtime capability that orders cross-boundary changes, captures the applied sequence, persists evolution metadata, and makes the path inspectable after the fact. Not control for its own sake, but architectural memory: the ability to answer "what happened, in what order, and was it what we intended?"
If behavior depends on accumulated change, then the order of those changes must be knowable and the applied sequence must be queryable. Cross-system mutations need to be observable, and convergence needs to be provable — not inferred from snapshots that happen to match.
Otherwise, you're validating outcomes and assuming history behaved.
What changes
Introducing an execution layer shifts how you reason about your systems. Evolution becomes an explicit, governed concern rather than an emergent one. Cross-boundary sequencing becomes deterministic. Divergence becomes something you diagnose from a ledger rather than reconstruct from logs. And audit stops being a retroactive exercise — it becomes inherent in how the system operates.
You stop debugging distributed side effects and start governing causality.
The real question
The question worth asking is not whether your tools apply changes correctly — most of them do. It's whether system evolution is a governed runtime concern in your architecture, or an emergent side effect of teams coordinating as best they can.
In distributed, multi-team, or regulated systems, that distinction compounds quickly. If the path shapes behavior, the path is architecture. The execution layer is what makes that architecture deterministic.
What comes next
In the next post, we'll look at what the structural requirements of an execution layer look like in practice — and where existing tooling ends and new architectural thinking begins.